We were in the process of finally getting DMARC fixed for all of our domains, and we had a supplier come and pitch PowerDMARC to us.
PowerDMARC, they told us, was the leading DMARC service in Norway, and was an ISO27001 certified provider headquartered in the United States.
After doing a quick trial with PowerDMARC we started with due dilligence, and the first red flags started to appear when trying to find company information.
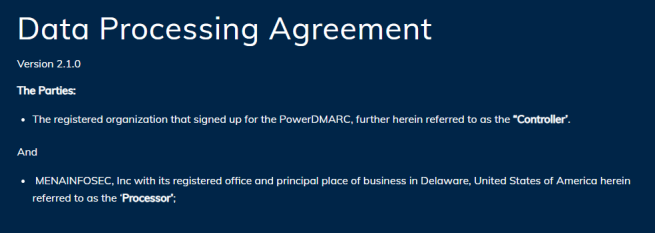
Their site mentions a head office address in Delaware, but the actual name of the company was only to be found in their Data Processing Agreement.
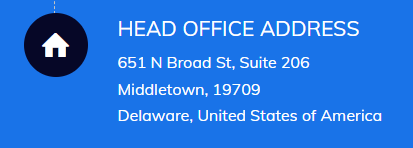
This led us to MENAINFOSEC, Inc., still listing it’s principal place of business to be Delaware in the United States.
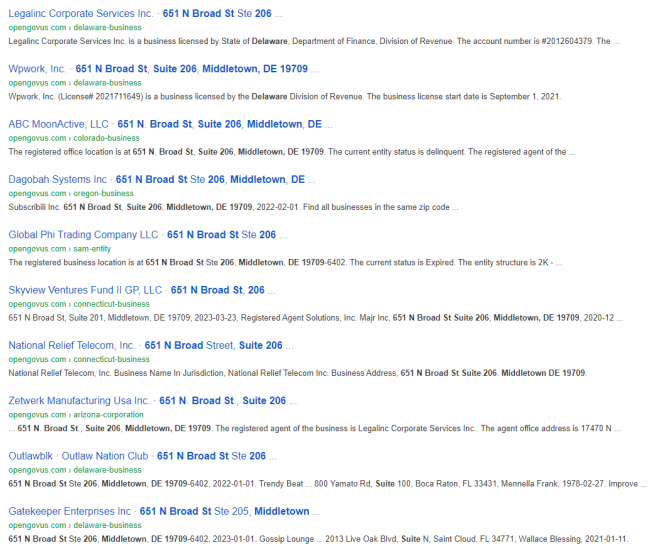
It turns out that 651 N Broad St in Middledown, Delaware is an anonymous office building, without any corporate logos. A few searches later makes it clear that this office building serves as a virtual office for several dozen other companies, and even several sharing Suite 206. Must be a crowded place.
Their LinkedIn profile doesn’t to much to help improve on the already shady first impressions, with only a single employee out of eighteen reporting to be based in Middletown.
So the company is not based in the US, and this throws their entire data processing agreement into jeopardy. But at least they’re ISO27001 certified, right?
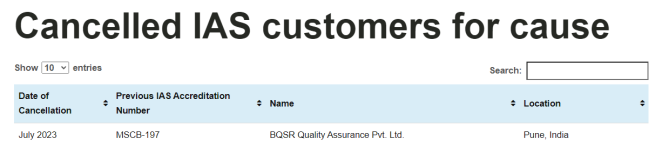
Well, it turns out that their certification body, BQSR Quality Assurance Pvt. Ltd., at least had their customer account with IAS (International Accreditation Service) canceled in july.
So it could be that PowerDMARC is a completely legit company, but there sure is a whole lot of smoke here.
Possible alternatives to PowerDMARC could be either dmarcian or uriports, but you should always vet your SaaS providers yourself.
